What Your Security Team Would See
Every blocked action is logged with full context: who, what, when, which policy rule, and which AI agent initiated it.
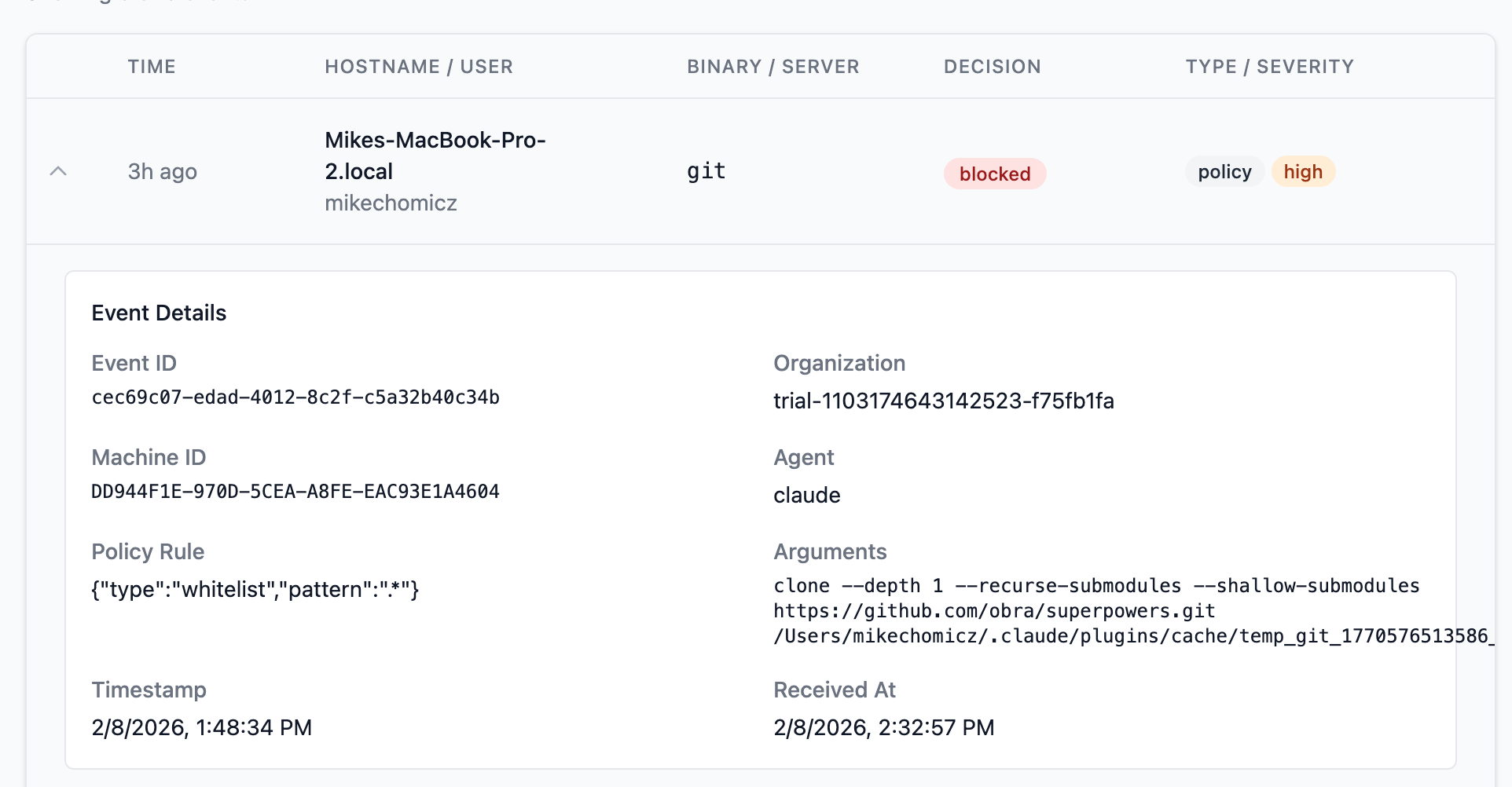
Audit Event: Plugin Clone Blocked
The dashboard shows the blocked git clone command with the exact arguments, the policy rule that matched (whitelist pattern), the AI agent that initiated it (Claude), the hostname, and the timestamp. Security teams get complete forensic context without asking the developer anything.
Intercepted
Truvant’s PATH shim intercepted the git clone before the shell executed it. The policy engine evaluated the command against the organization’s security policy.
Blocked & Logged
The command was denied. A structured audit event was written locally and sent to the management console with full context: binary, arguments, policy rule, agent, user, and hostname.
Visible to Security
The security team sees the event in the Truvant dashboard immediately — filterable by severity, binary, hostname, and decision. No developer action required.